Neither version of Windows, either Windows XP, Windows 7, or 8 or more modern versions such as Windows Server 2008 or Windows 2012, provides an SSH server to use a standard way to access from other machines with different operating system and be able to run console commands, copy files, forward ports or automate logins by using public/private keys. The Microsoft alternative to this is WinRM / Powershell, but many are the chances that we will need to find a standard and compatible way to access to other systems, and what better way to do this than using the widespread and well-known SSH protocol to get into our Windows machines securely.
Error: Your Requested widget " ai_widget-6" is not in the widget list.
- [do_widget_area above-nav-left]
- [do_widget_area above-nav-right]
- [do_widget_area footer-1]
- [do_widget id="wpp-4"]
- [do_widget_area footer-2]
- [do_widget id="recent-posts-4"]
- [do_widget_area footer-3]
- [do_widget id="recent-comments-3"]
- [do_widget_area footer-4]
- [do_widget id="archives-4"]
- [do_widget_area logo-bar]
- [do_widget id="oxywidgetwpml-3"]
- [do_widget_area menu-bar]
- [do_widget id="search-3"]
- [do_widget_area sidebar]
- [do_widget id="search-4"]
- [do_widget id="ai_widget-2"]
- [do_widget id="categories-5"]
- [do_widget id="ai_widget-3"]
- [do_widget id="ai_widget-4"]
- [do_widget id="ai_widget-5"]
- [do_widget_area sub-footer-1]
- [do_widget id="text-4"]
- [do_widget_area sub-footer-2]
- [do_widget_area sub-footer-3]
- [do_widget_area sub-footer-4]
- [do_widget_area upper-footer-1]
- [do_widget id="search-2"]
- [do_widget id="recent-posts-2"]
- [do_widget id="recent-comments-2"]
- [do_widget id="archives-2"]
- [do_widget id="categories-2"]
- [do_widget id="meta-2"]
- [do_widget_area upper-footer-2]
- [do_widget_area upper-footer-3]
- [do_widget_area upper-footer-4]
- [do_widget_area widgets_for_shortcodes]
- [do_widget id="search-5"]
- [do_widget id="ai_widget-6"]
- [do_widget_area wp_inactive_widgets]
- [do_widget id="wpp-2"]
- [do_widget id="text-1"]
- [do_widget id="recent-posts-3"]
- [do_widget id="categories-3"]
- [do_widget id="archives-3"]
- [do_widget id="icl_lang_sel_widget-3"]
FreeSSHd, a free SSH server for Windows
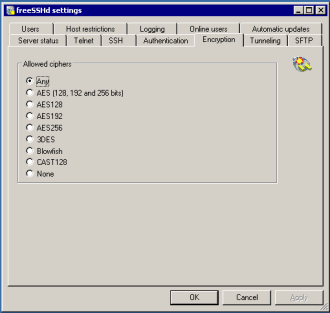
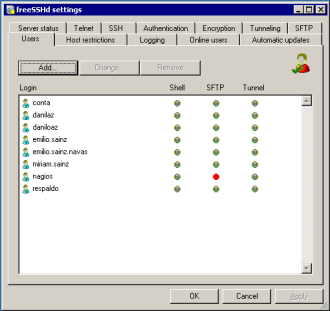
Although other alternative SSH softwares for Windows, mostly commercial but also some free ones, freeSSHd is a very simple setup SSH server and gives very good results. It provides strong encryption and username/password or public/private key authentication features, also allowing secure file transfer via FTP/FTPS/SFTP protocols and tunneling connections via port forwarding. That is basically all we can find in OpenSSH.
Installing and configuring freeSSHd
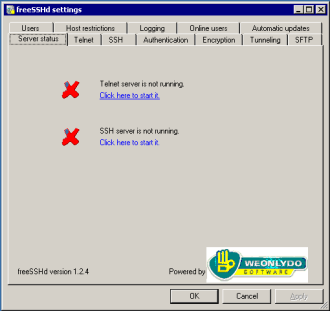
Once downloaded and installed the application in the usual way, run it and find a control panel like that one in the following screenshot. The first step we must take to configure the SSH server is to start it up as a Windows service that runs in the background (SSH server is not running. Click here to start it.).
Open the port 22 on windows firewall
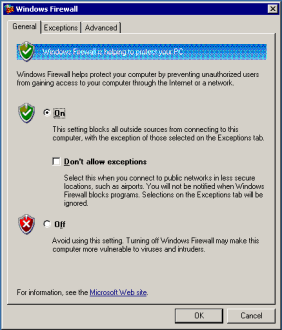
To reach our new SSH server from outside we need the port 22 (or that one you choose in settings) is open and there is no restriction to establish connections against it. By default, the Windows Firewall blocks such connections, so you must explicitly authorize them:
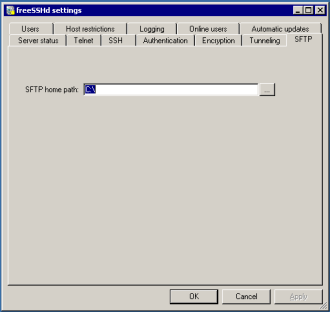
Secure file transfer via SFTP
freeSSHd also acts as a secure FTP server, enabling secure file transfers via FTP/FTPS/SFTP protocols. As these protocols use the underlaying SSH connection, we don’t have to do anything special to configure them. Just setting the root directory for our files and using an appropriate client against the recently open port 22, we’ll be able to perform secure file transfers.
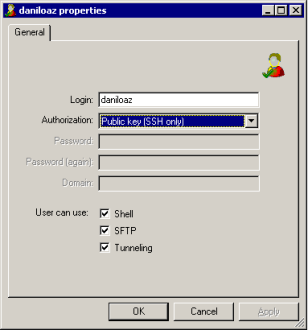
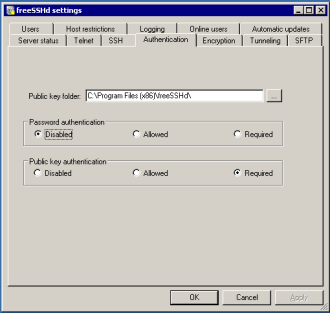
Access by public key
One of the huge advantages of SSH is that it provides automated access to our server with no need to enter username and password every time. Just generating a new pair of private and public keys for our user, or assigning an existing one we can just enter the command console or copy files to our server in one click.
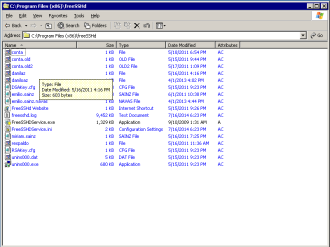
To achieve this we’ll indicate to freeSSHd which is the directory where the public keys of different users are stored. By default the installation directory will be used. There we’ll copy one file for each user whose name is simply the name of that user without any extension. Each of these files must contain only the public key for that user. Private keys should not be stored in any way on the server, but only in the SSH client we use to connect with.
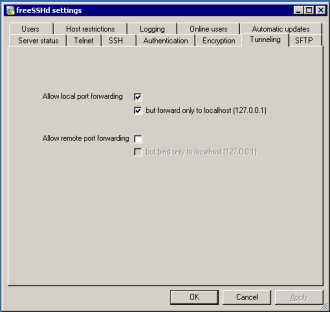
Port fordwarding
Another interesting freeSSHd feature: it provides tunneling connections from other ports/services that have nothing to do only using the SSH secure access. That is, we could establish a connection to Windows Terminal Server via RDP protocol over port 3389 (non-secure connection) leveraging our SSH access and with no need to open the port 3389 on our firewall. Moreover, although RDP traffic is not encrypted, it will travel safely across the Internet as it is encapsulated into SSH packets that are strongly encrypted. In this way we’ll gain much in safety and simplicity, as we can establish all connections to our server services only opening port 22 on our firewall and can concentrate all our efforts on SSH security and monitoring without having to worry about the different protocols and ports handled by our applications.


Leave a Reply