The terraform import command allows you to import into HashiCorp Terraform resources that already existed previously in the provider we are working with, in this case AWS. However, it only allows you to import those records one by one, with one run of terraform import at a time. This, apart from being extremely tedious, in some situations becomes impractical. This is the case for the records of a Route53 DNS zone. The task can become unmanageable if we have multiple DNS zones, each one with tens or hundreds of records. In this article I offer you a bash script that will allow you to import in Terraform all the records of a Route53 DNS zone in a matter of seconds or a few minutes.
Script to automatically change all gp2 volumes to gp3 with aws-cli
Last December Amazon announced its new EBS gp3 volumes, which offer better performance and a cost saving of 20% compared to those that have been used until now (gp2). Well, after successfully testing these new volumes with multiple clients, I can do nothing but recommend their use, because they are all advantages and in these 2 and a half months that have passed since the announcement I have not noticed any problems or side effects.
How to automatically update all your AWS EC2 security groups when your dynamic IP changes
One of the biggest annoyances when working with AWS and your Internet connection has a dynamic IP is that when it changes, you immediately stop accessing to all servers and services protected by an EC2 security group whose rules only allow traffic to certain specific IP’s instead of allowing open connections to everyone (0.0.0.0.0/0).
15 Tips and Tools for Successful Remote Working after Covid-19
There are many people and companies that due to the coronavirus crisis (Covid-19) are being forced to adopt different forms of remote working these days. As an architect of cloud solutions (Cloud Computing) and freelance system administrator I have been working this way successfully for many years, so some of them are asking me during the last days advice on what strategies to follow and what useful applications exist to manage to telecommuting efficiently. That is why I decided to go a step further and write this article in which I compile a series of recommendations and tools that I hope will help many people who are forced to perform their work remotely from home in these new coronavirus era. However I also hope all those people and companies that see an opportunity in all this and choose to bet definitely for remote work, either partially or fully, will find it useful too.
Linux remote control from your smartphone via SSH button widgets
In this post I will tell you about an Android app that is extremely useful to run commands remotely on a Linux computer: Hot Button SSH Command Widget. This application allows you to launch conveniently any command you want on a remote computer through SSH only with the push of a button on the screen of your mobile phone or tablet. This not only will facilitate automation of repetitive tasks, but also is very interesting from the perspective of security for the same reasons I exposed in my Automatically lock/unlock your screen by Bluetooth device proximity post. It will allow you for example to lock and unlock the screen without having to type your password again and again in sight of other people.
How to exclude your own [dynamic] ip from Google Analytics
In my 5 ways to exclude your own visits from Google Analytics post I discussed the 5 main methods that exist to prevent visits you make to your own websites are tracked by Google Analytics, each with its pros and cons. However, I found it necessary to further expand the first of those methods, which in my opinion is the best possible way to exclude your own internal traffic from Google Analytics based on your IP address, whether fixed or dynamic. It allows you not only to block yourself but also filter the activity of all members on your own team or company, which is of utmost importance to avoid any interference with data collected from real user activity.
And I say Google Analytics because it is the main actor in this market, but this same method is perfectly suitable for any other web analytics tool like Piwik, Clicky, OWA, Clicktale, StatCounter, Kissmetrics, Mouseflow and many others.
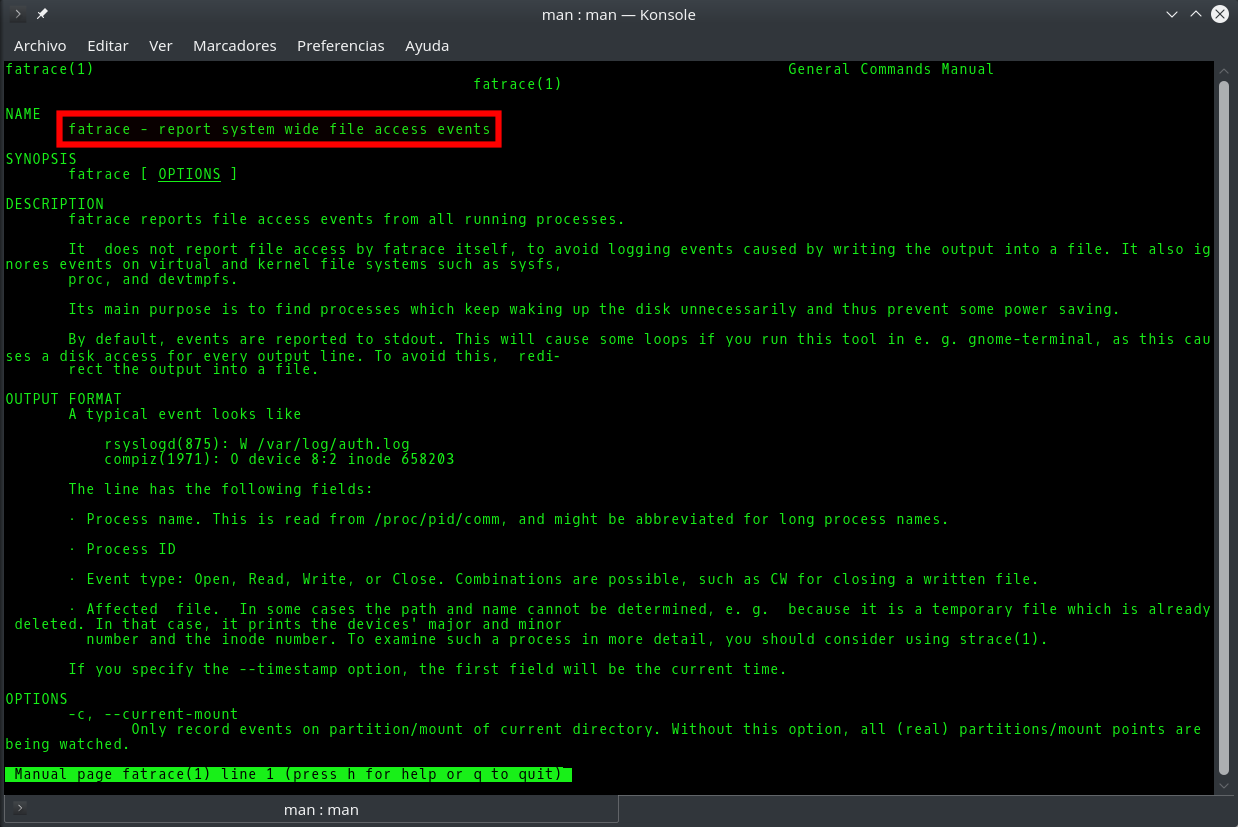
Fatrace command: how to know in real time which processes are writing to a file
It is usually easy to know which process or processes are writing to a given file in Linux, since we either know its origin and its nature beforehand (for example the Apache access_log), or we can easily find it out with the fuser or lsof commands. However, sometimes it will happen that although we know the role and purpose of a file, there are so many applications accesing it simultaneously that it is very difficult to know which of them is the one that reads/writes the most or does so in a precise moment. Knowing this would be very useful to learn for example why a log file is growing excessively or which application is making an abusive use of system resources, either by mistake or intentionally.
Unlock Linux command line after pressing Ctrl+s in Bash





![How to exclude your own [dynamic] ip from Google Analytics](https://cdn.daniloaz.com/wp-content/uploads/2017/06/page-analytics-chrome-extension.jpg)